Coinbase Text Scam – Don’t Fall for Fake Crypto Messages

Author: Adam Collins
So, you're just living your life, scrolling through memes, ordering pizza, and suddenly—buzz. A text message pops up. It looks like it’s from Coinbase.
But wait—you don’t even have a Coinbase account!
And that, my friends, is exactly the point.
Welcome to the world of the Coinbase Text Scam (also called a Coinbase scam text or Coinbase text message scam). It’s so common that many crypto newbies run into it at some point. Think of it as today’s version of the old “Is your fridge running?” prank call—except this one is trying to steal your Bitcoin, not your punchline.
The Anatomy of a Crypto Text Scam
This scam is a type of smishing—aka SMS phishing. Instead of emailing you, scammers send texts that feel more urgent and personal. That’s why it’s sometimes called the Coinbase login scam text or the Coinbase withdrawal code text scam.
Here’s what these fake messages often say:
⚠ Urgent: A withdrawal of $5,000 in BTC has been approved from your Coinbase account. If this was not you, click here immediately.
⚠ Your Coinbase account has been locked due to suspicious activity. Verify your identity at this link to restore access.
⚠ You’ve received a payment of [insert ridiculously high amount of crypto here]. Claim it now!
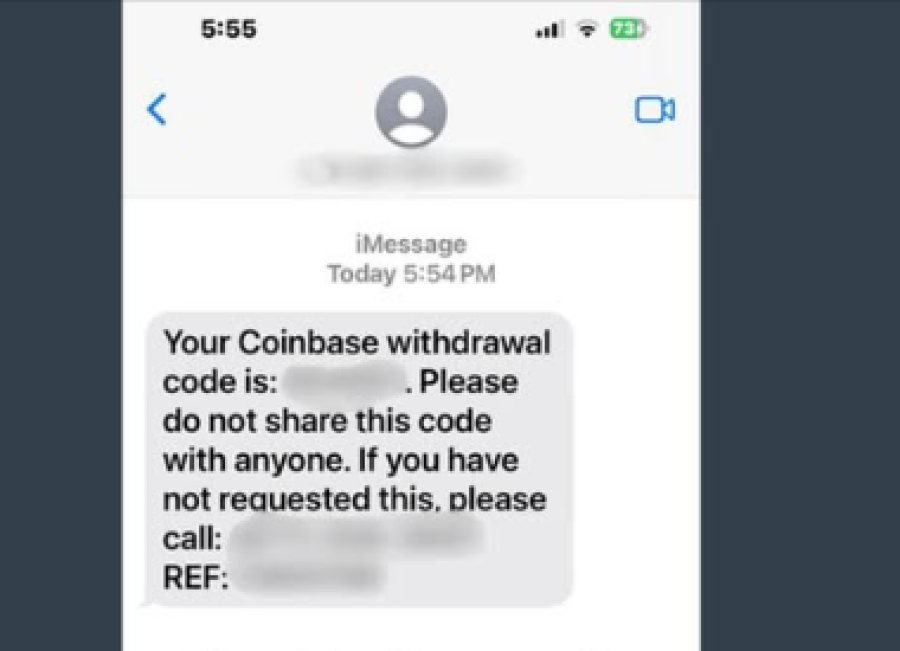
Source: Facebook
Notice the trick? Every message is designed to spark fear (“your money is gone”) or greed (“you just got free Bitcoin”). That emotional push makes people click without thinking—and that’s exactly how these crypto scams work.
How to Spot a Coinbase Scam Text
Here’s your no-nonsense guide to catching a Bitcoin scam before it catches you:
🚩 They Don’t Know You
Most of these scam texts go out at random. The scammer doesn’t know if you’re a crypto whale or just someone collecting bottle caps. If you don’t even have a Coinbase account, that’s already a huge red flag.
🚩 The Panic Button Trap
If the text is screaming “act now!” or “urgent security issue,” your alarm bells should ring. Real Coinbase security doesn’t work like that. Legit companies don’t use pressure tactics in text messages.
🚩 The URL of Doom
Fake Coinbase texts almost always include shady links. They’ll look like:
- www-coinbase.com
- colnbase.com
- coinbase.net
If it’s not exactly https://www.coinbase.com, it’s a trap. Bookmark the real Coinbase site and always use that.
🚩 The “We’ll Never Ask” Rule
Coinbase will never ask you for:
- Your password
- Your 2FA codes
- Your private keys
If a text or call asks for any of this, it’s a pure Coinbase phishing scam.
🚩 Grammar Gone Wrong
A lot of scam texts read like a bad movie script—awkward words, weird punctuation, and clumsy grammar. If it feels off, it probably is.
What to Do If You Get a Coinbase Scam Text
Don’t panic, don’t click, don’t reply. Just ignore it.
Report it:
- Screenshot the message and send it to security@coinbase.com
- Forward it to 7726 (SPAM) in the U.S. to help block future attacks.
- Delete it and move on like the crypto hero you are.
By reporting, you’re not just protecting yourself—you’re helping stop these crypto text scams from spreading to others.
Bottom Line: Install ScamAdviser App
The Coinbase text scam is one of the most common crypto scams out there. Whether it’s a Coinbase withdrawal code text scam, a fake Coinbase login scam text, or just another random Bitcoin scam, the rules stay the same:
- Don’t click suspicious links
- Don’t share private info
- Always go directly to the official Coinbase security page or app
🚩 Extra tip: Before you visit or download from an unknown website, check it on ScamAdviser.com. You can search domains, phone numbers, IBANs, crypto wallets—the whole scammy ecosystem.
On mobile? The ScamAdviser app, Android or iOS version, is your pocket-sized safety net. Download it and browse smarter.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if