Crypto Recovery Scams: How to Avoid Getting Scammed Twice

Author: Adam Collins
Imagine losing thousands in a crypto scam. You’re angry, confused, desperate and just when you think it can’t get worse, someone messages you promising to get your crypto back. It sounds like hope… but it’s actually another trap.
Welcome to the world of crypto recovery scams, where fraudsters prey on people who’ve already been scammed once. If you're trying to reclaim crypto, this guide will help you understand how these double scams work, how to spot the red flags, and what legitimate steps you can take instead.
Round One: The Original Scam That Started It All
Before we talk about recovery scams, let’s rewind. These are the most common ways people lose crypto in the first place:
- Pig butchering scams: A long con where a scammer builds trust over weeks or months before convincing victims to “invest” in fake crypto schemes.
- Romance scams: Love and lies—scammers pretend to fall for you, then convince you to send them crypto.
- Investment scam crypto platforms: Flashy websites that promise guaranteed returns. Spoiler: they disappear the moment you “invest.”
- Phishing scam crypto: Fake websites or messages that trick you into handing over your wallet info.
- Rug pulls: Developers hype a project, raise money, and vanish with your funds. Remember CryptoZoo, the infamous Paul Logan game?
- Crypto wallet drainer attacks: Clicking the wrong link can install malware that drains your wallet.
- Fake crypto exchanges and fake crypto experts: They look legit. They're not.
These scams leave victims crushed and vulnerable to the next deception.
Round Two: The Crypto Recovery Scam
When people lose money to crypto fraud, they understandably want it back. That’s where crypto recovery scams swoop in, pretending to help, but are designed to scam you again.
Here’s how these fraudulent recovery companies typically operate:
- They contact you out of the blue (social media, email, online forums).
- They promise 100% success in stolen crypto recovery (red flag alert).
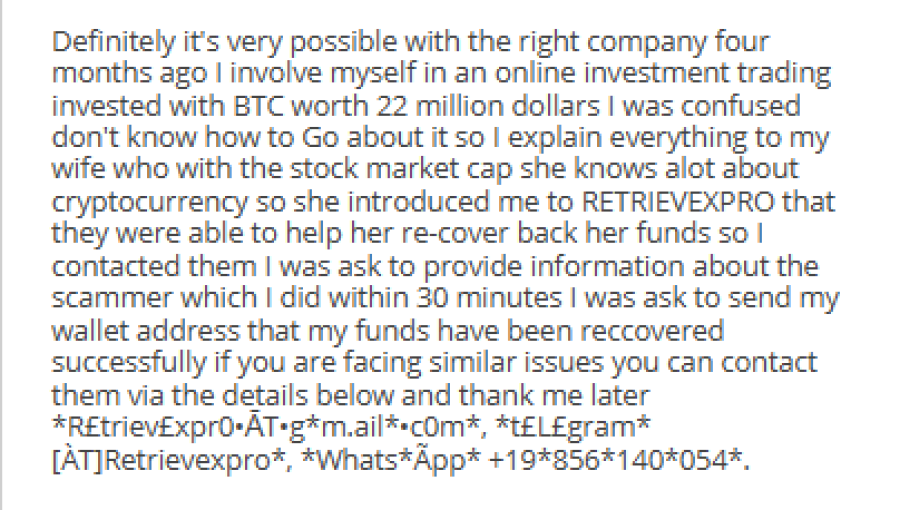
Example of a Crypto Recovery Scam
- They ask for upfront fees before doing anything — classic advance fee scam.
- They claim they can “hack” wallets or have “inside access” to exchanges (they don’t — and that would be illegal).
- They ask for your private keys or seed phrases. Major no-no.
- They use pressure tactics to rush you into decisions.
- Their websites look sketchy or generic, with fake testimonials and no real contact info.
- Some even say your funds are recovered but need “release fees” or “crypto taxes” before you get them. Spoiler: you won’t.
If you’re already hurting from the first scam, it’s heartbreaking to fall into this second trap.
Spotting the Red Flags
Here’s your quick-reference guide to spotting a fake crypto recovery service:
🚩 Guarantees of recovery – No one can promise to recover crypto. Blockchain transactions are irreversible.
🚩 Upfront fees – If they want money first, walk away.
🚩 Requests for private keys/seed phrases – This is like giving someone the keys to your house and hoping they return the TV they stole.
🚩 Unrealistic claims – Anyone saying they can “hack back” your funds is lying or breaking the law.
🚩 Vague methods – “We have special tools” or “inside connections” isn’t a plan. It’s a script.
🚩 Urgency tactics – “Act now or lose your funds forever!” This is fear-mongering, not help.
🚩 Poor online presence – No legit business only lives on WhatsApp.
🚩 Too-good-to-be-true testimonials – Search independent review sites, not just what they show you.
Remember: Legitimate crypto recovery services don’t make promises and don’t ask for sensitive info or upfront payments.
Scammed Already? Here's What to Actually Do
If you’ve lost crypto in a scam, here’s how to respond safely and smartly:
Step 1: Lock It Down
- Change all passwords and enable two-factor authentication (2FA).
- Move any remaining crypto to a secure wallet (preferably a hardware wallet).
Step 2: Collect the Evidence
- Save transaction IDs, wallet addresses, screenshots, and chats with scammers or fake recovery agents.
Step 3: Stop Communicating
- Don’t respond to the scammer.
- Don’t engage with random recovery “experts” who slide into your DMs.
Step 4: Report It
- Report crypto scam to local police.
- File with national agencies like:
-
- FBI’s Internet Crime Complaint Center (IC3)
- FTC (Federal Trade Commission)
- National consumer protection bodies.
- Contact the crypto exchange involved.
- Share your story on forums to warn others.
Step 5: Be Realistic
It’s tough to get crypto back after a scam. The blockchain doesn’t do refunds. Cryptocurrency tracing through blockchain forensics might locate your funds, but that doesn’t mean you’ll recover them. Even law enforcement crypto scam investigations often hit a wall.
What Might Help — Legitimate (but Limited) Options
- Law enforcement: Still your best shot, especially if the scammers are operating within a jurisdiction.
- Blockchain analysis firms: They can trace funds, but they can’t recover them.
- Legal advice: If your loss is substantial, a lawyer specializing in digital assets might help explore options.
- Self-recovery tools: Lost your wallet password or seed phrase? There are legit services for that. But if your crypto was stolen… recovery is unlikely.
So, is crypto recoverable? Sometimes — but rarely. And never through someone who DMs you a miracle.
Bottom Line: Prevention Is Power
The best way to reclaim crypto is to never lose it in the first place.
✅ Educate yourself: Learn the latest scam tactics.
✅ Research everything: Platforms, exchanges, apps — dig deep.
✅ Secure your wallets: Use hardware wallets, strong passwords, and 2FA.
✅ Trust your gut: If it sounds too good to be true, it is.
These habits help you prevent crypto scams and protect what’s yours.
Final Word: Knowledge Beats Scammers
Crypto can be exciting, innovative, and empowering. But it also attracts scammers, especially those who target people twice.
First they steal your crypto.
Then they steal your hope.
Don’t let them win.
If you’ve been scammed, take the right steps. Stay skeptical, stay informed, and don’t let one mistake turn into two. Because in crypto, as in life, knowing who not to trust is half the battle.
FAQs
What are crypto recovery scams?
Crypto recovery scams are frauds that target victims of previous crypto scams by promising to recover their stolen funds, usually in exchange for upfront fees or personal wallet details.
Can stolen crypto be recovered?
In most cases, stolen crypto is very difficult to recover due to the irreversible nature of blockchain transactions. Some funds may be traced using blockchain forensics, but actual recovery is rare.
What are the red flags of a fake crypto recovery service?
Guaranteed results, upfront fees, requests for private keys or seed phrases, vague methods, and pressure to act quickly are all common red flags.
Are there any legitimate crypto recovery services?
Legitimate services, like blockchain forensics firms or legal experts, may help trace stolen funds or advise on legal action. However, they do not guarantee recovery and never ask for sensitive information upfront.
What should I do if I’ve already been scammed?
Secure your accounts, gather all evidence, report the scam to law enforcement and crypto platforms, and avoid unsolicited recovery offers.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if
