Filmyzilla Review: Is FilmyZilla34.com Safe or Illegal?
Author: Adam Collins
In a Nutshell
- Identify the "domain hopping" pattern used to bypass legal takedowns.
- Recognize that recent registrations like FilmyZilla34.com signal temporary, high-risk mirrors.
- Avoid clicking fake "Download" buttons that trigger intrusive tracking scripts.
- Prioritize legal streaming platforms to ensure your data and device remain secure.
Domain registration records on Whois & ScamAdviser show that FilmyZilla34.com appeared on the web on August 26, 2025. This follows a long history of similar domains, including the original FilmyZilla.com which dates back to March 6, 2017. If you are searching for a way to watch the latest hits without a subscription, you have likely landed on one of these many variants. You are looking for a movie, but you might be finding a digital trap instead.
Track the redirect maze
Scammers use redirects—automatically sending you from one URL to another—to stay ahead of security filters that block known malicious links. Watch your browser's address bar as you attempt to navigate the site. You will often see the URL flash through variations like Filmyzilla28.com, Filmyzilla30.com, or Filmyzilla32.com before you reach your destination.
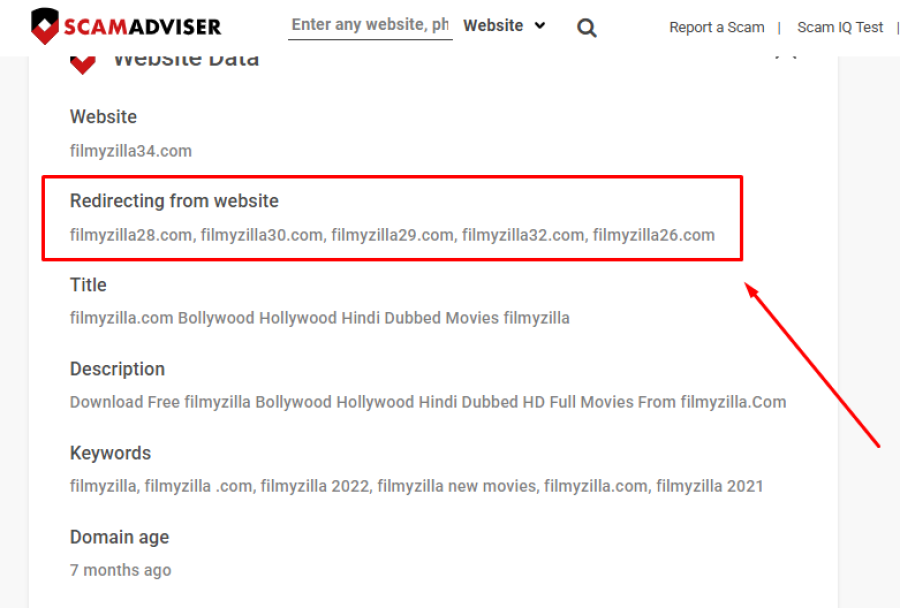
This constant shifting is a hallmark of piracy networks. When a domain like Filmyzilla26.com gets flagged by authorities, the owners simply move the content to Filmyzilla29.com. This keeps the site active, but it also means you never know who is truly operating the site you are visiting. If a site cannot maintain a stable home, you cannot trust what it is putting on your hard drive.
Verify the registration dates
Legitimate businesses rarely change their primary domain, but piracy networks frequently abandon old URLs to avoid legal enforcement. Compare the history of the original FilmyZilla.com, registered in 2017, with the much newer FilmyZilla34.com, which appeared on August 26, 2025. This massive gap suggests that the newer site is likely a clone or a temporary mirror designed to capture traffic while the original faces legal pressure.
Check the WHOIS data—a public database that lists the ownership details and registration dates of a domain—whenever you encounter a "top" site. A domain that is only a few months old but claims to be a long-standing authority is a major red flag. If the site owners are hiding their identity behind recent registrations, they have no accountability if your device gets infected.
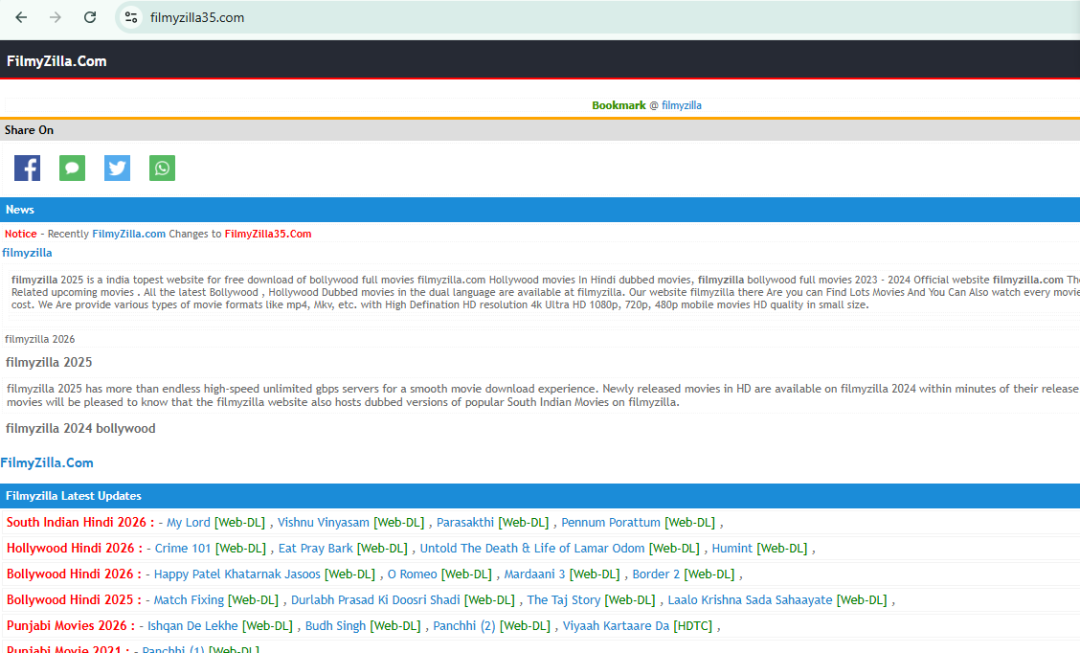
Evaluate the "topest" claim
Professional websites invest in quality control and clear communication, whereas fly-by-night operations often use awkward phrasing to mimic popular search terms. Look closely at the site’s self-description as "India’s topest website for free download of Bollywood full movies." While the grammar might make you chuckle, it is a sign that the site is built for search engine algorithms rather than human users.
Whether FilmyZilla.com is legal or illegal is not much of a mystery when you see these claims. Distributing copyrighted Bollywood movies for free without a license is a violation of international copyright laws. These sites do not pay the creators, which is why they have to hide behind a rotating network of domains to stay online.
Spot the download traps
Malicious sites hide malware—software designed to damage or gain unauthorized access to your computer—behind fake buttons that look like legitimate movie links. Hover your mouse over any "Download Now" button without clicking to see the destination URL. If the link leads to an executable file ending in .exe or .zip instead of a video format like .mp4, you are about to download a virus.
The free Bollywood movie download site risks go beyond just viruses. These platforms often use aggressive ad networks that track your browsing habits and personal data. You might think you are getting a free movie, but you are actually paying with your privacy and the health of your computer.
Common Red Flags
- A "Topest" claim or other broken English in official descriptions.
- Rapidly changing numbers in the domain name (e.g., Filmyzilla 28, 29, 30).
- Hidden WHOIS information or very recent registration dates for an "established" site.
- Multiple pop-ups and redirects before you can see any actual content.
If you want to watch Bollywood films safely, stick to verified platforms. Services like Netflix, Amazon Prime Video, Disney+ Hotstar, and Zee5 offer massive libraries of Bollywood content legally. Many also offer free, ad-supported tiers or trial periods that are much safer than a suspicious download link.
You can report suspicious websites to the National Cyber Crime Reporting Portal or verify them using the ScamAdviser app. Protecting your digital identity is more important than watching a movie for free.
This article has been written by a scam fighter volunteer. If you believe the article above contains inaccuracies or needs to include relevant information, please contact ScamAdviser.com using this form.
Adam Collins is a cybersecurity researcher at ScamAdviser who operates under a pseudonym for privacy and security. With over four years on the digital frontlines and 1,500+ days spent deconstructing thousands of fraud schemes, he specialises in translating complex threats into actionable advice. His mission: exposing red flags so you can navigate the web with confidence.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if

