How to Recognize a Fake Online Shop
Author: Adam Collins
In a Nutshell
- The Age Test: Use a WHOIS tool to see when the site was born. If it’s only a few days old, it’s a red flag.
- The Payment Rule: Never use Zelle, Wire Transfers, or Crypto. Stick to Credit Cards for protection.
- The AI Check: Look for "dead" social media buttons and AI-generated "owners" who never seem to blink.
- The Price Reality: If the discount is more than 70% off a premium brand, you aren't the customer; you're the victim.
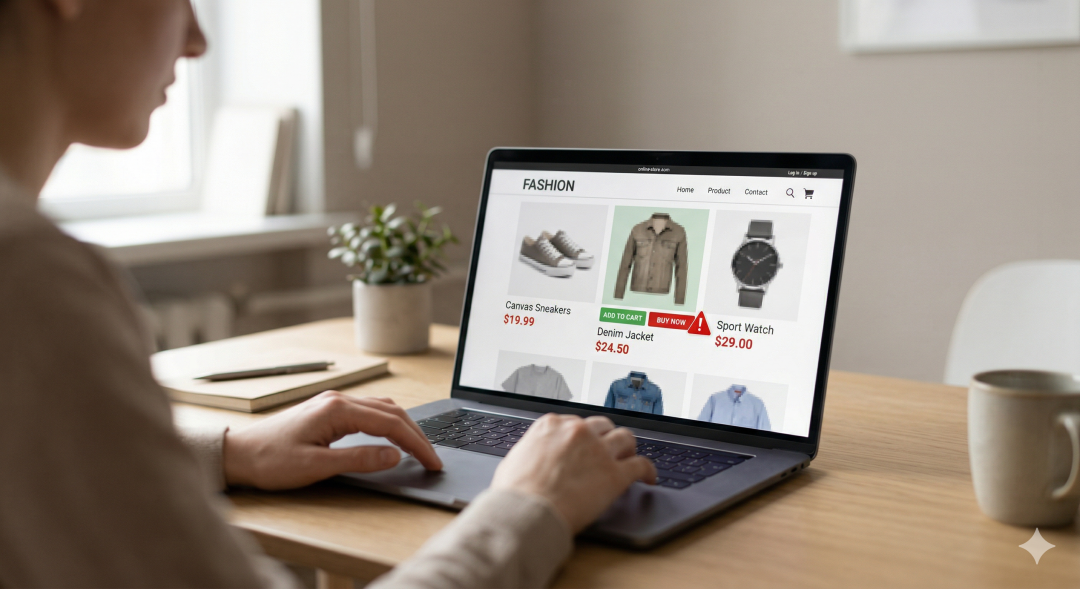
We’ve all been there: you’re scrolling through TikTok or Instagram and see an ad for a North Face jacket or a Stanley tumbler at 80% off. It looks legit, the site looks professional, and that "limited time" countdown is ticking.
But here’s the reality check: In 2025 alone, shoppers lost nearly $16 billion to fraud. These aren't just "bad businesses"—they are sophisticated digital traps designed to harvest your credit card info or ship you a box of literal trash.
Here is how you can stay ahead of the scammers.
How to Spot the Trap
Modern scammers have traded clunky websites for AI-powered "clones" that look identical to the brands you trust. They use stolen imagery and professional templates to lower your guard. Here is what to look for:
1. Inspect the "Birth Date"
Scammers launch sites, steal as much as possible, and shut down before they get caught. Use a public WHOIS database to check the URL. If a "Big Brand Outlet" was registered three weeks ago, close the tab immediately.
2. Hunt for AI Glitches
In the age of deepfakes, scammers use AI to create fake "About Us" stories and videos.
The Blink Test: In video ads, watch the eyes. AI often struggles with natural blinking patterns.
The Social Loop: Click the Instagram or Facebook icons at the bottom of the page. On fake sites, these icons usually just refresh the page or lead to a "404 Not Found" error.
3. Audit the Checkout Options
Credit cards offer chargebacks, which is a scammer's worst enemy. That’s why they’ll try to steer you toward "non-reversible" methods like:
Peer-to-peer apps (Zelle, Venmo, CashApp)
Cryptocurrency
Gift cards
Bank wire transfers
4. The "Fine Print" Fail
Scammers are lazy with text. Read the "Shipping & Returns" policy. You’ll often find mentions of a completely different company name or nonsensical grammar that was copy-pasted from a different scam template.
The Bottom Line: If its too good, it is
If a deal feels like a gift, you aren't finding a bargain—you're being targeted. Scammers exploit the trust we place in social media ads to bypass our skepticism. The best defense is to slow down: if the price is too good to be true, the website is almost certainly a lie. For the latest official data and reporting tools, check the FTC’s Guide on Avoiding Online Shopping Scams.
Frequently Asked Questions
Q: The site has a padlock icon. Doesn't that mean it's safe?
A: No. The padlock (SSL certificate) only means the data sent between you and the site is encrypted. It does not prove the business is legitimate. In fact, most phishing sites now use SSL to look professional.
Q: What if I already entered my card info but didn't finish the purchase?
A: You should still call your bank. Some fake sites use "form-jacking" software that captures what you type into the boxes in real-time, even if you never hit the "submit" button.
Q: Can I trust "Verified Buyer" reviews on the site?
A: Not on a site you don't recognize. Scammers use "review farms" to flood their pages with fake 5-star testimonials. Always check independent platforms like Scamadviser to see the real trust score of a domain before buying.
Q: I was scammed. How do I get my money back?
A: If you used a credit card, call your bank immediately to file a fraudulent transaction claim. If you paid via Zelle or wire transfer, the money is likely gone, but you should still report it to help authorities track the scammers.
If the price is too good to be true, the website is almost certainly a lie. Download the ScamAdviser app.
Adam Collins is a cybersecurity researcher at ScamAdviser who operates under a pseudonym for privacy and security. With over four years on the digital frontlines and 1,500+ days spent deconstructing thousands of fraud schemes, he specialises in translating complex threats into actionable advice. His mission: exposing red flags so you can navigate the web with confidence.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if

