How to Recognize a Phishing Scam
Author: Adam Collins
In a Nutshell
- Verify the sender’s full email address to catch "lookalike" domains or subtle typos.
- Hover your cursor over every link to see the actual web destination before you click.
- Treat "perfect" grammar with caution; modern AI allows scammers to mimic professional brand tones flawlessly.
- Beware of "MFA Fatigue"; never approve a login notification you didn't personally trigger.
- Report suspicious activity to the FTC, CISA, or your provider’s security team.
In 2025, the FBI’s Internet Crime Complaint Center (IC3) reported that phishing remains the most prevalent cyber threat, with complaints exceeding 193,000 annually in the U.S. alone. While complaint volumes have stabilized, the financial impact has skyrocketed, with total reported cybercrime losses hitting a record $16.6 billion in the last year.
You are the primary target because, in an era of hardened servers, humans remain the "softest" entry point. Phishing has evolved beyond simple emails into a multi-channel assault:
- Smishing: Malicious SMS texts (now 70% of mobile-based attacks).
- Vishing: Voice phishing, now powered by AI voice cloning to mimic executives or family members.
- Quishing: The use of malicious QR codes in emails to bypass traditional security filters (up 400% since 2023).
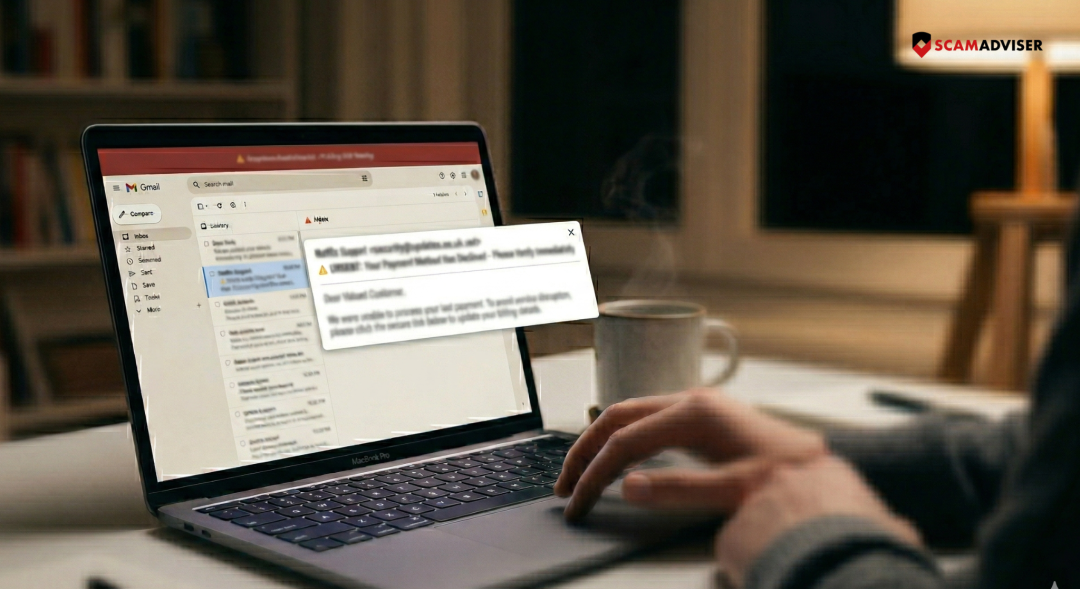
Identify the Spoofed Sender
Scammers hide behind "display names" while the actual address is a random string. They use "lookalike" domains—like @support-paypal.com instead of @paypal.com.
Now: Attackers now use "Subdomain Hijacking," where they send emails from legitimate but compromised subdomains of famous brands to bypass "Safe Sender" lists.
Check for Link Discrepancies
A button may say "Verify Account," but the underlying code directs you to a credential-harvesting site.
On a computer, hover your mouse over the link to see the destination in the bottom corner of your browser. On mobile, long-press the link to preview the URL. If it doesn't match the company’s official domain, it is a scam.
Spot the Urgency & "MFA Fatigue" Traps
Phishing relies on "forced errors" created by artificial deadlines. Scammers use phrases like "unauthorized login detected" or "action required within 4 hours."
Now: Scammers now utilize MFA Fatigue attacks, where they bombard your phone with dozens of multi-factor authentication prompts, hoping you will click "Approve" just to stop the notifications. Never approve an MFA prompt you did not initiate.
Scrutinize Grammar (The AI Factor)
Older advice suggested looking for "broken English." This is outdated. With the rise of Generative AI, scammers now produce typo-free, professional, and brand-consistent communications in any language. Instead of looking for spelling errors, look for contextual errors: Is this a service you actually use? Is the request for information unusual?
Question Unexpected Attachments & QR Codes
Attachments remain a primary delivery vehicle for malware. However, Quishing (QR Phishing) is the new frontier. Scammers embed QR codes in emails because many security filters cannot "read" the link inside an image. If an email asks you to "Scan this code to secure your account," it is almost certainly a trap.
Verify Requests for Credentials
Legitimate companies will never ask for your password, Social Security number, or full credit card details via email or text. If a message directs you to a login page, close the message and navigate to the website manually by typing the address into your browser.
If You’ve Been Targeted
- Change Passwords: Update credentials for the affected account and any other account using the same password.
- Enable Passkeys or Hardware MFA: Use physical security keys (like YubiKeys) which are significantly more resistant to modern phishing than SMS codes.
- Report It: Forward phishing emails to reportphishing@apwg.org or use the "Report Junk" feature in your email client. For smishing, forward the text to 7726 (SPAM).
If a link feels even slightly suspicious, do not click it—verify the site's reputation on ScamAdviser first.
Adam Collins is a cybersecurity researcher at ScamAdviser who operates under a pseudonym for privacy and security. With over four years on the digital frontlines and 1,500+ days spent deconstructing thousands of fraud schemes, he specialises in translating complex threats into actionable advice. His mission: exposing red flags so you can navigate the web with confidence.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if
