Is Aagmaal.com Safe? Watch XXX Videos Safely

Author: Adam Collins
In a Nutshell
- Registered in 2020 and active for several years
- Connected to multiple redirecting domains
- Heavy advertising and pop-ups increase risk
- Possible exposure to malware and tracking
- Extra security is needed before visiting
Aagmaal.com is a popular search term for users looking for fast-loading, full-HD Indian adult videos. Known by many as AAG Maal, the site promises easy navigation, quick access, and free explicit content without complicated sign-ups.
At first glance, it seems convenient. Videos load fast, the layout is simple, and there’s no obvious paywall. But convenience in the adult streaming world often comes with hidden risks. That’s why many users still ask the same question: Is Aagmaal.com safe, or is it putting your device and privacy at risk?
Let’s break it down.
What is Aagmaal.com?
Aagmaal.com is an adult entertainment website that mainly focuses on Indian and Desi porn content. It offers explicit videos in HD quality and promotes itself as a simple, no-hassle platform.
Many users are drawn to the site because it doesn’t require accounts, subscriptions, or payments. You click, you watch, and you move on. However, this “free and easy” model depends heavily on advertising networks, and that’s where most problems begin.
When Was Aagmaal.com Registered?
According to WHOIS and ScamAdviser records, Aagmaal.com was registered on August 28, 2020.
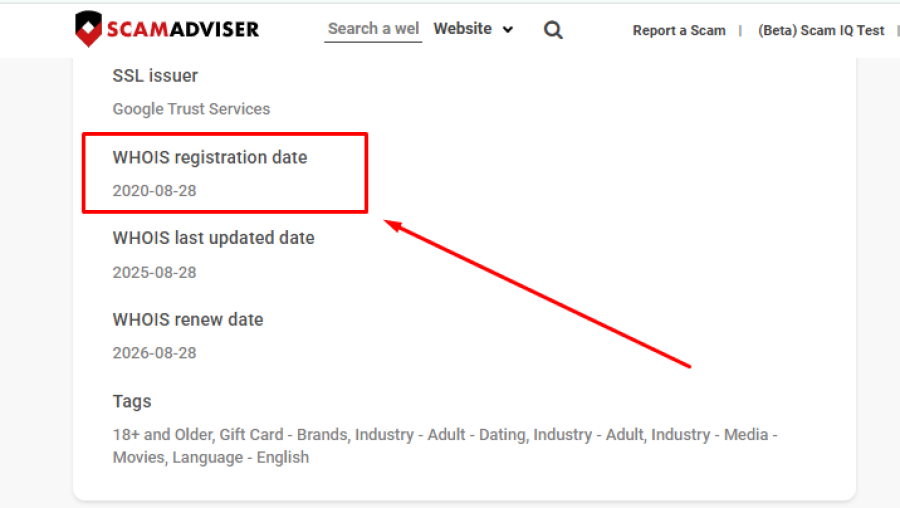
This means the website has been online for several years, which can sometimes indicate stability. Scam sites often disappear quickly, while long-running domains may seem more trustworthy.
However, in the adult content space, domain age alone is not a guarantee of safety. Many risky platforms survive for years by constantly switching domains and monetizing traffic through aggressive ads.
The Redirecting Problem: Why Aagmaal Keeps Changing Domains
One of the biggest warning signs around Aagmaal.com is its connection to multiple similar domains, including versions like Aagmaal.one and Aagmaal.site.
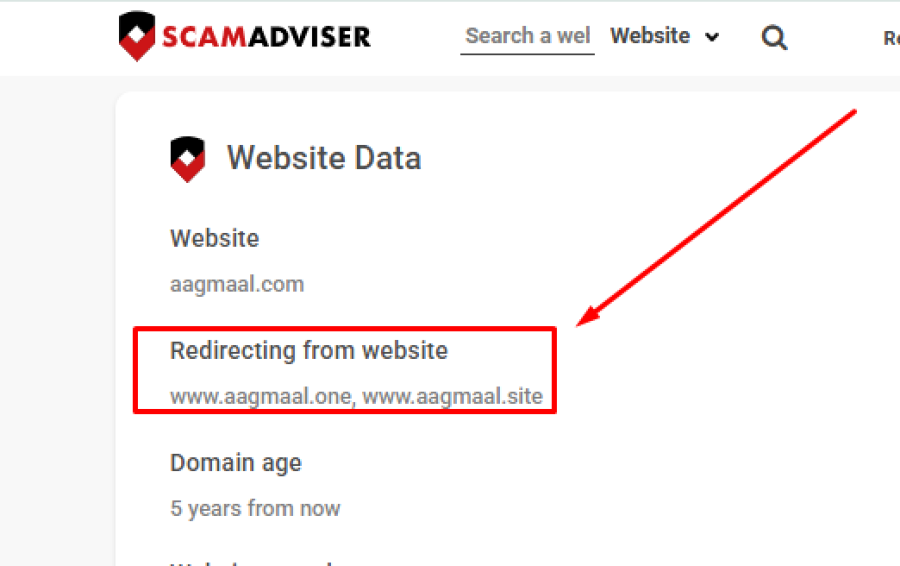
There is a possibility that clicking on videos, thumbnails, or buttons may take you to completely different websites.
These redirects are rarely random. They are usually designed to send users to advertising partners, adult networks, fake subscription pages, or even phishing sites. Because of this, you may never be fully sure where you are being taken or who controls the destination.
This makes browsing unpredictable and increases the risk of landing on unsafe pages.
Can You Get Malware From Porn Websites?
Yes, and this is a serious concern.
Adult websites are among the most commonly abused platforms for spreading harmful software. Because traffic is high and users are often clicking quickly, scammers use these sites to hide malicious ads and fake buttons.
On platforms like Aagmaal.com, the most common dangers come from disguised “Play” buttons, fake download prompts, and misleading pop-ups. Some pages may try to convince you that your device needs an update or that you must install a special video player.
In reality, these downloads usually contain adware, spyware, or browser hijackers.
Even without downloading anything, harmful scripts can sometimes run in the background if you interact with the wrong advertisement.
Is Aagmaal.com Legit or Just Risky?
Aagmaal.com does appear to host real adult content. Many visitors confirm that videos play as expected and that the site is not simply pretending to offer content.
So, it’s not a classic “fake” website.
However, being real does not mean being safe.
The frequent redirects, unclear ownership, heavy advertising, and lack of transparency make it a high-risk environment. The site focuses more on monetizing traffic than on protecting users.
In simple terms, it works, but it comes with strings attached.
How to Watch Porn on Aagmaal.com More Safely
If you still choose to visit Aagmaal.com, you should take extra precautions.
Using reliable antivirus software is essential. This helps block known malicious scripts and dangerous pop-ups before they load. A strong ad blocker also makes a big difference, since most threats arrive through advertisements.
Never download anything offered by the site. If a page tells you to install a player, update, or app, leave immediately. That is almost always a scam.
You should also avoid entering personal information. Email addresses, phone numbers, and payment details should never be shared on adult streaming sites or redirected pages.
Using private browsing mode can help limit tracking cookies, and keeping your browser updated reduces the chance of security exploits.
These steps won’t make the site completely safe, but they lower your exposure.
Privacy Concerns: What Happens to Your Data?
Most adult websites, including Aagmaal.com, do not clearly explain how user data is handled.
Behind the scenes, many rely on third-party ad networks that collect browsing behavior, device information, and location data. This information may later be used to target you with scam ads, adult subscriptions, or misleading offers.
If privacy is important to you, this lack of transparency is another reason to be cautious.
Bottom Line: Is Aagmaal.com Safe?
Overall, users get what they look for in adult websites, porno videos, but at what cost?
- Aagmaal.com hosts real adult content and has been active since 2020
- Redirects and mirror domains increase security risks
- Malware and scam ads are possible
- Privacy protections are unclear
- Safe browsing requires strong protection tools
This article has been written by a scam fighter volunteer. If you believe the article above contains inaccuracies or needs to include relevant information, please contact ScamAdviser.com using this form.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if
