SlotMega & BadakWin Exposed: The “Mega” Slot Network Secret
Author: Adam Collins
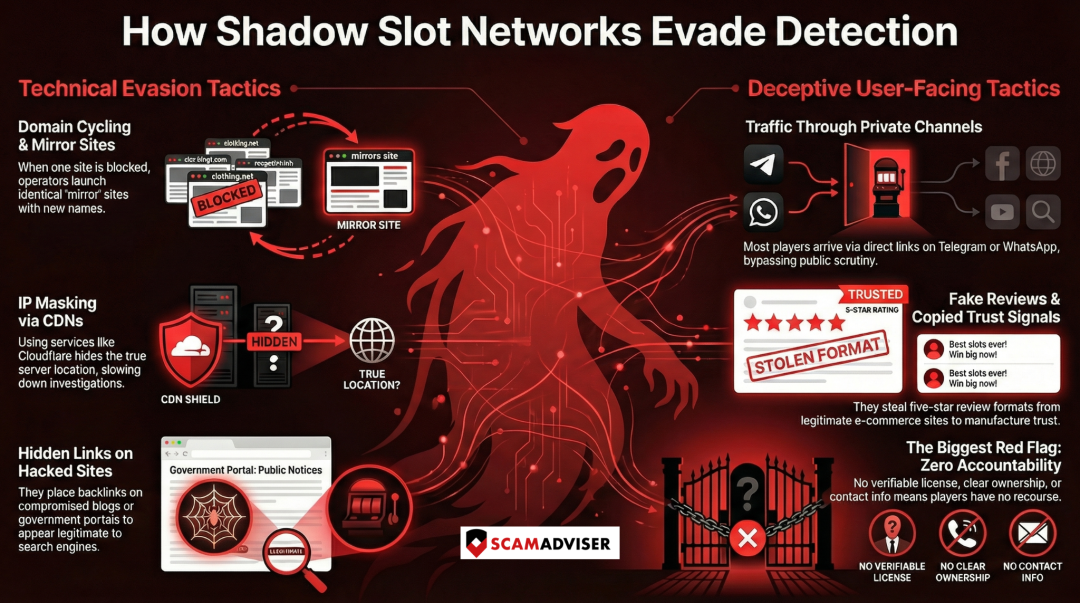
In a nutshell:
- Mega slot sites survive by cycling domains and using mirror websites
- Familiar names and designs are used to create false trust
- IP masking hides the real operators
- Traffic is pushed through Telegram and private channels
- Fake reviews replace real credibility
- No license means no accountability
- The ScamAdviser app helps flag risky sites before you deposit
These slot sites do not survive by accident. They use a set of well-tested tactics designed to stay one step ahead of blocks, complaints, and regulators. Once you recognize the pattern, the names matter far less than the methods.
Domain Cycling and Mirror Sites
One of the most common tricks is domain cycling. When a gambling site is blocked or reported, operators simply launch a new version under a slightly different name. Sometimes it is just a number added at the end. Other times it is a small spelling change or a different extension.
This is why players often see names like slotgacor1, slotgacor2, or slotgacorvip appear within days of each other. These are not competitors. They are mirrors. Traffic is quietly redirected, Telegram groups are updated, and the old domain is abandoned without explanation.
For players, this creates confusion. A site that looks familiar feels safe, even when the domain itself is brand new.
IP Masking and Content Delivery Networks
Another layer of protection comes from IP masking. A large portion of illegal gambling sites use content delivery networks such as Cloudflare. While these services are legitimate and widely used, they also make it harder to identify where a site is actually hosted.
Instead of revealing the real server location, visitors and authorities only see the CDN’s infrastructure. This slows down enforcement and makes takedowns far more complicated. By the time one site is investigated, several others are already live.
For users, this means the site can look technically “secure” while hiding who really operates it.
Traffic Through Telegram and Private Channels
Unlike legitimate businesses, these sites do not rely heavily on search engines. Most traffic comes through Telegram groups, WhatsApp broadcasts, and social media posts. Influencers and affiliate accounts share direct links that bypass public filters and blocks.
This method has two advantages. First, links can be replaced instantly when one stops working. Second, users arriving through private channels are less likely to research the site beforehand. The focus is on speed, bonuses, and urgency.
By the time doubts appear, money is already deposited.
Compromised Domains and Hidden Backlinks
In many cases, the site name does not appear openly on its own. Instead, it shows up as a hidden or embedded link on unrelated websites. These can include abandoned blogs, hacked pages, or even high authority domains such as educational or government portals in different countries.
This is a known black hat SEO tactic. It helps gambling sites appear more legitimate to search engines while staying under the radar. To a user, the link looks out of place. To an algorithm, it looks trustworthy.
The result is visibility without accountability.
Fake Reviews and Copied Trust Signals
Search results linked to these domains often include five-star reviews, “star seller” labels, or testimonials that look convincing at first glance. On closer inspection, many of these are copied word for word from legitimate e-commerce platforms.
The goal is simple. Borrow trust from brands people already recognize. When users see familiar language and review formats, skepticism drops. Very few stop to check where the reviews actually came from.
Trust is manufactured, not earned.
No Licensing and no Clear Ownership
Perhaps the biggest red flag is what is missing. There is no verifiable gambling license. No registered business entity. No clear ownership structure. Contact details are vague, temporary, or routed through messaging apps only.
Without licensing or transparency, there is no real accountability. If a withdrawal is blocked or a site disappears, there is nowhere to escalate the issue. That is not a technical problem. It is a design choice.
Bottom line: Be Careful When Gambling
You do not need to be a tech expert to stay safe. Patterns like domain cycling, hidden ownership, and private traffic channels are red flags anyone can learn to spot. The ScamAdviser app makes this easier by helping you check websites in seconds and avoid high-risk gambling platforms.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if

