Top Scams Making Headlines: Fake Rentals, Crypto Fraud, and Tractor Cons

Author: Adam Collins
What you’ll learn in this article:
- Fake apartment ads on social media are tricking renters into paying upfront fees.
- Sophisticated crypto scams are stealing millions with phishing and impersonation.
- Farmers and buyers are falling victim to fake websites selling tractors and machinery.
- Scams can happen to anyone—protect yourself with tools like the ScamAdviser app and official resources like the Federal Trade Commission.
What’s going on with fake apartment rental ads?
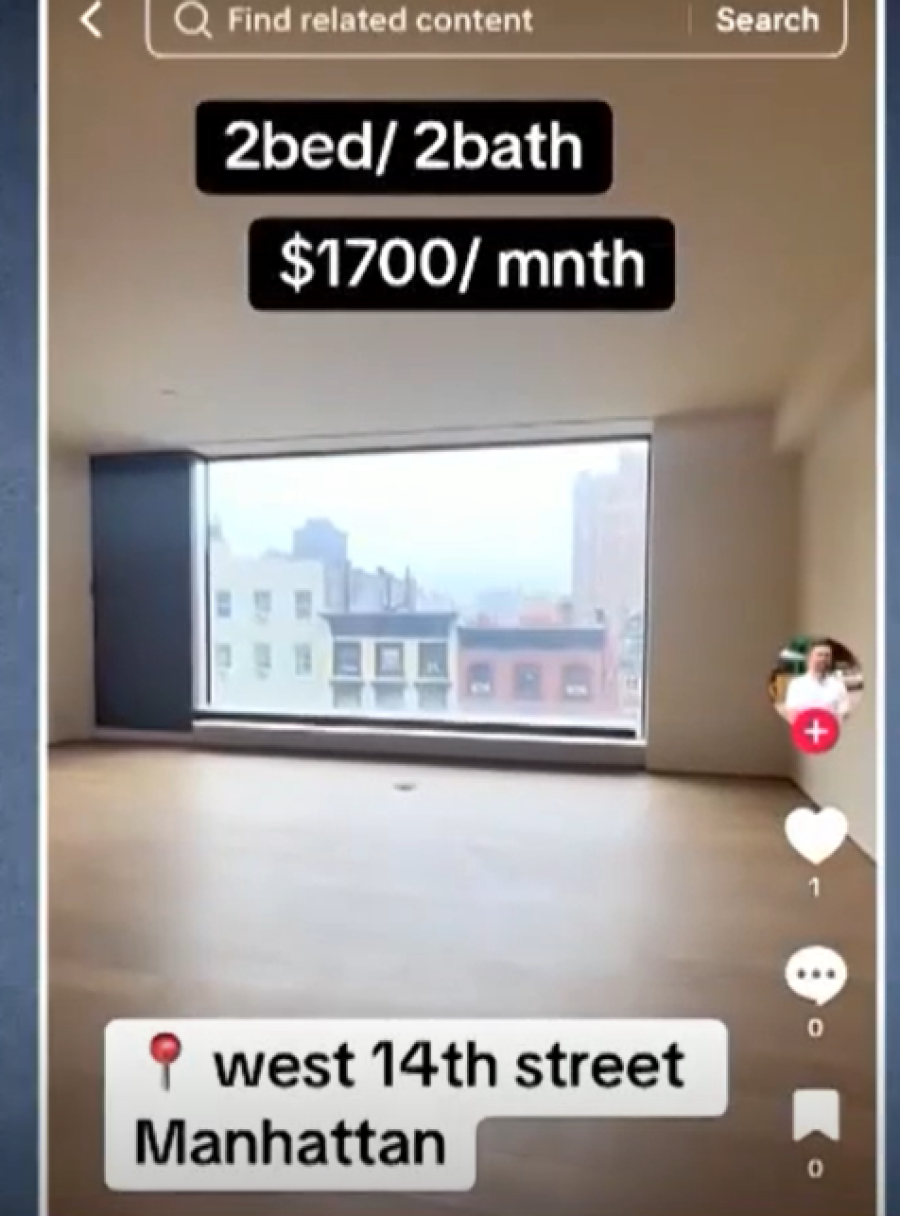
Scammers are flooding social media with apartment listings that look almost too good to be true—because they are. These ads often include slick videos and gorgeous images, but here’s the catch: the apartments don’t exist.
How the scam works:
- You spot a trendy apartment on Instagram, TikTok, or Facebook.
- The price is way below market, so you get excited.
- The “landlord” asks you to pay upfront fees such as application, deposit, or first month’s rent.
- Once you pay, the scammer disappears and you never see the apartment.
How to avoid it:
- Always see the apartment in person before paying.
- Search the images online to check if they’re stolen from another listing.
- Verify the property with a trusted realtor or landlord.
- Use reliable scam-checking tools like ScamAdviser.
How are scammers pulling off crypto fraud?
In one recent case, a victim in Wales lost £2.1 million in bitcoin after being duped into entering their password on a fake website. The scammers didn’t stop there—they pretended to be senior U.K. police officers and convinced the victim they were helping with a security issue.
Why this scam is so dangerous:
- It is highly targeted, often using personal data from real breaches.
- Scammers impersonate trusted authorities such as police, bank officials, or government officers.
- Once your crypto is transferred, recovery is almost impossible.
Red flag phrases scammers often use:
- “Your account has been compromised.”
- “We detected unusual activity—act now.”
- “Transfer your funds to a secure wallet immediately.”
- “I’m calling from law enforcement, and this is urgent.”
- “Failure to respond could result in account suspension.”
How to protect yourself From Crypto Scams:
Never enter your credentials on a site you reached through an email or message.
- Double-check URLs—fake sites often look nearly identical to real ones.
- Use two-factor authentication on all your accounts.
- Learn more about data security from trusted sources like Stanford University’s Cybersecurity Center.
What’s the deal with tractor scams?
It’s not just city renters and crypto investors being targeted—farmers are too. A 61-year-old farmer in Essex thought he was buying a John Deere 6430 tractor online. The website looked legitimate, complete with dealership branding and listings. He wired nearly £30,000, only to later find out the site was a perfect clone of a real French dealership.
Signs it was a scam:
- The website had real-looking stock listings but no real inventory.
- Payment was requested upfront, with little buyer protection.
- A friend traveling to pick up the tractor discovered the dealership had never heard of the sale.
Lessons learned:
- Always verify the dealership directly before wiring large sums.
- Be wary of sites that look polished but have no verifiable history.
- If possible, use escrow or secure payment systems.
Bottom Line: Scams Come for Us All
Whether you’re house-hunting, investing in crypto, or shopping for farming equipment, scammers are lurking. They thrive on urgency, fake authority, and tempting deals.
Protect yourself by staying skeptical of deals that feel “too good,” using tools like ScamAdviser to check a site’s trustworthiness, and relying on official guidance from trusted resources like the FTC.
Download the ScamAdviser app today and get scam alerts before scammers get you.
Frequently Asked Questions
What are fake apartment rental scams?
Fake apartment scams appear on social media with attractive listings and videos. Victims are asked to pay upfront fees for deposits or applications, but the apartments don’t exist.
How do cryptocurrency scams work?
Crypto scams often involve phishing websites and impersonation. Victims are tricked into entering credentials or sending crypto to scammers, who may pose as police or bank officials.
What is a tractor buying scam?
Scammers clone legitimate farm equipment dealerships online, post fake tractor listings, and request upfront payments. Victims only realize it’s a scam when the dealership denies any record of the sale.
How can I protect myself from these scams?
Verify listings, double-check websites, avoid upfront payments to strangers, and use tools like ScamAdviser. For government-backed resources, check the FTC’s scam prevention page.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if
