WEBxSERIES.ac | WEBxSERIES.to: Free Indian XXX Videos or a Trap?

Author: Adam Collins
If you’ve been searching for free Indian 18+ web series, chances are you’ve already landed on WEBxSERIES.ac or one of its many mirrors like .to, .io, or .com. You clicked for one simple reason: no signup, no payment, no limits. Just endless “hot” web series, instant streaming, and zero barriers. At first glance, it feels like you’ve hit the jackpot. The site even presents itself as one of the oldest and most trusted names in the space, claiming to have served users from 2019 to 2026.
But here’s the uncomfortable truth, most people only discover too late. Behind that tempting “Play” button may be aggressive pop-ups, silent trackers, and hidden scripts designed to squeeze data, and sometimes money, out of you. Before you get pulled in, there are several technical red flags and domain patterns you need to know about.
False Longevity: When Was WEBxSERIES Registered?

The site’s marketing suggests a long-standing history of providing daily content for over six years. However, a look at the domain registration data reveals a different story that might be worth noting:
- WEBxSERIES.ac: Registered February 16, 2026.
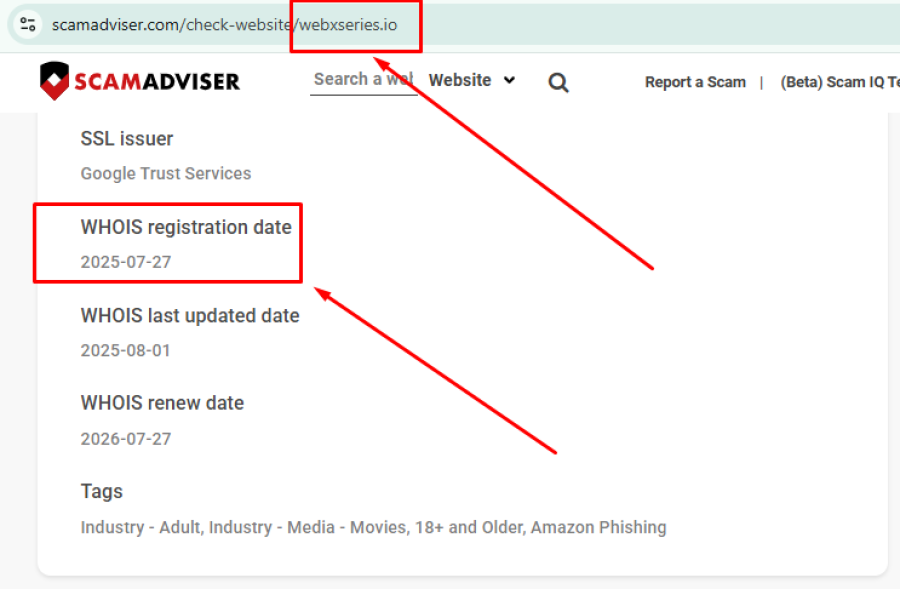
- WEBxSERIES.io: Registered July 20, 2025.
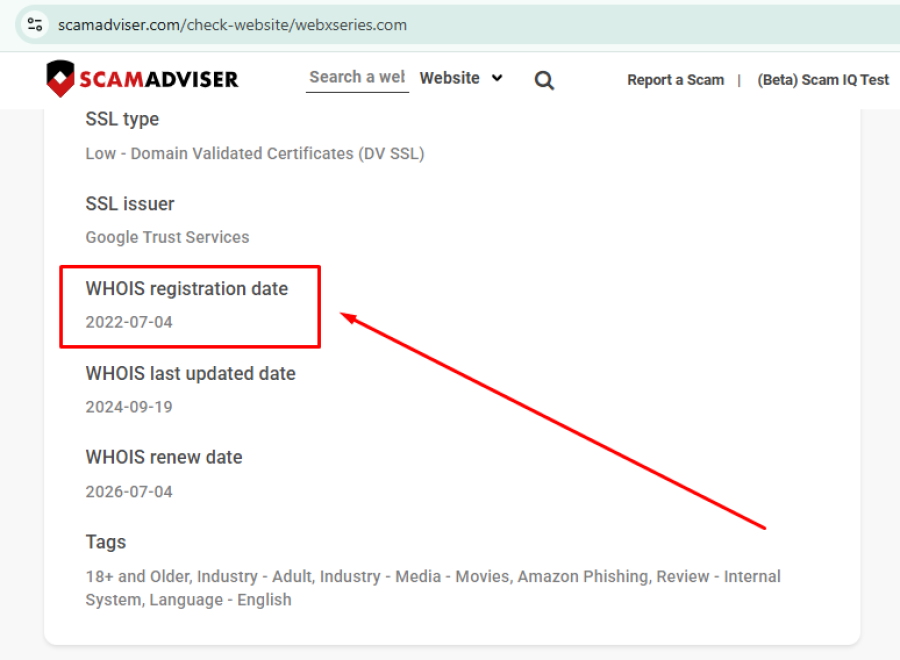
- WEBxSERIES.com: Registered July 04, 2022.
While the brand name may have existed previously, the primary domain currently being promoted is essentially brand new. This pattern of shifting from one extension to another is often seen when platforms face technical hurdles, ISP blocks, or security flags. The discrepancy between the claimed "seniority" and the actual age of the URLs is a common characteristic of high-risk sites.
The Redirect Maze
Users often report being bounced between various extensions like .ac, .to, .net, and .com. This "domain hopping" is frequently a tell-tale sign that a platform is attempting to stay ahead of automated filters or legal scrutiny. For the average visitor, these constant redirects can be confusing and may lead to destinations that were not originally intended.
Content and Copyright Questions
It appears highly probable that WEBxSERIES does not produce the majority of the content it hosts. Much of the material seems to be aggregated from premium streaming services and independent creators. This likely places the site in the category of a piracy aggregator rather than a licensed distributor. Because the platform likely operates without official distribution rights, there is often a lack of transparency regarding how user data is handled or who is actually running the backend.
Malware and Malvertising Concerns
A significant concern with sites of this nature is the advertising ecosystem they employ. Since mainstream ad networks generally avoid unregulated adult sites, these platforms often turn to high-risk providers. This can lead to:
- Aggressive Redirects: Clicking a video might trigger a script that opens multiple windows for gambling or "device repair" services.
- Suspicious Downloads: Buttons that look like "Play" or "HD Quality" could potentially be masks for unwanted software or browser extensions.
- Tracking Scripts: There is a high possibility that these pages contain invisible trackers designed to monitor browsing habits for third-party data brokers.
Is WEBxSERIES Safe to Visit?
When looking at the full picture—the hidden ownership, the very recent domain registrations, and the likely use of pirated content—there are several factors that suggest a high level of risk. While the site might provide the videos it promises, it appears highly possible that doing so exposes your device to malware or invasive tracking.
The reliance on aggressive ad networks and the constant switching of domains are patterns frequently associated with platforms that prioritize traffic over user security.
Bottom Line: Should You Trust WEBxSERIES?
Approaching WEBxSERIES requires a high degree of caution. It fits a specific profile of adult aggregation sites that operate in a legal gray area and utilize high-risk monetization methods. The lack of clear ownership and the recent creation dates for their "old" service suggest that all may not be as it seems.
Before visiting, it is highly advisable to use updated security software and consider whether the "free" content is worth the potential compromise of your digital privacy.
This article has been written by a scam fighter volunteer. If you believe the article above contains inaccuracies or needs to include relevant information, please contact ScamAdviser.com using this form.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if
