Gelatin Trick Recipe for Weight Loss by Jillian Michaels: Real or A Scam?

Author: De-Reviews.com Team
The internet is flooded with posts promoting Gelatin Trick Recipe for Weight Loss by Jillian Michaels. These ads promise unbelievable results, sometimes claiming users can lose dozens of pounds in days. Social media, blogs, and YouTube videos suggest Jillian Michaels invented this secret recipe, creating a sense of credibility. But after a careful review of promotional content, websites, and Jillian Michaels’ own statements, it becomes clear that most of these claims are highly questionable.
While the gelatin trick concept itself has a real dietary basis, the way it’s presented online through manipulated videos, hidden recipes, and pre-packaged supplements raises serious red flags.
Red Flags in the Online Promotions:
A closer inspection of the ads, videos, and sales pages reveals multiple problematic elements that suggest these offers may not be real:
1. Misuse of Jillian Michaels’ Image:
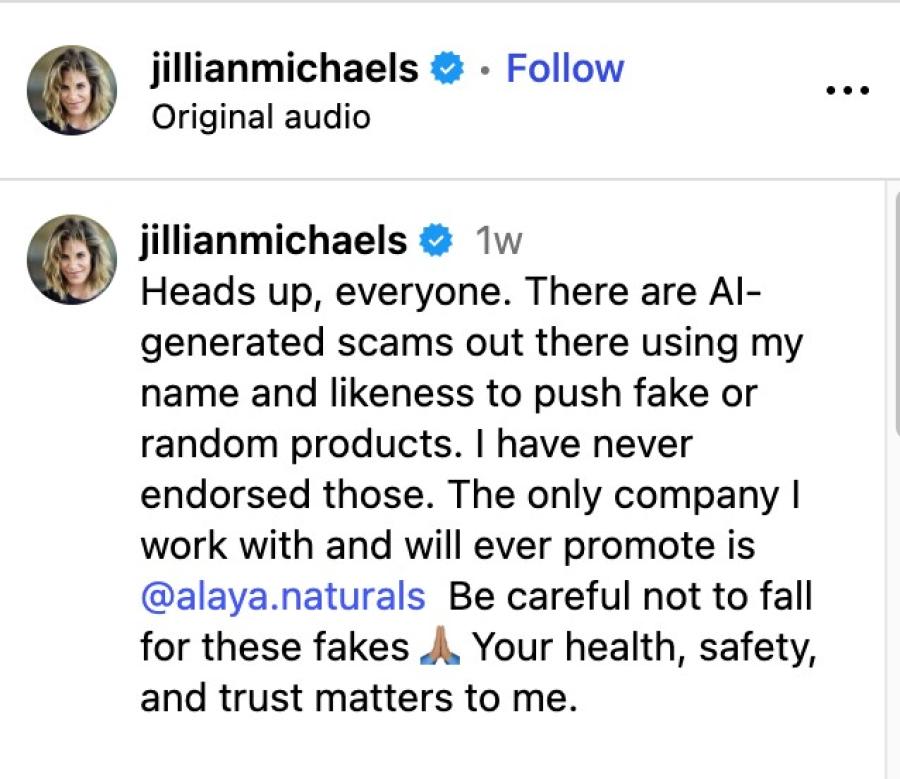
One of the most concerning points is that these promotions misuse Jillian Michaels’ likeness and name. The videos often appear to show Jillian discussing the “secret gelatin trick” on TV or social media. However, the footage has been manipulated with AI-generated voiceovers and edited scripts to give the impression that she endorses the product. Jillian Michaels herself addressed this on Instagram:
"Heads up, everyone. There are AI-generated scams out there using my name and likeness to push fake or random products. I have never endorsed those. The only company I work with and will ever promote is @alaya.naturals Be careful not to fall for these fakes 🙏🏽 Your health, safety, and trust matters to me."
This is a critical warning. Any online claim suggesting Jillian Michaels invented or endorses secret gelatin trick recipe should be viewed as highly questionable.
2. Hidden Recipes and Misleading Videos:
The YouTube videos promoting the gelatin trick create a sense of anticipation but never reveal the actual recipe. They often include:
- Long videos with fake progress bars, making viewers feel like the secret is just about to be revealed.
- Emotional stories about miraculous weight loss, often with celebrities or regular people, but with no real evidence.
- Redirects to sales pages for supplements instead of providing the actual gelatin recipe.
The so called secret ingredient is never clearly explained. Instead, viewers are encouraged to buy pre-packaged capsules or supplements that are supposed to contain the right ingredients.
3. Overhyped Claims and Pressure Tactics:
The marketing around “secret gelatin trick recipe” is loaded with questionable credibility boosters:
- Fake urgency messages like limited stock, today only, or 35 people viewing this page right now.
- Unverifiable five star reviews, often claiming tens of thousands of customers. For example, some pages claim 76,000 reviews but provide no evidence or sources for these ratings.
- Claims that the product not only supports weight loss but also helps with joint pain, which does not match the original story of a miracle gelatin recipe.
4. Questionable Website Credibility:
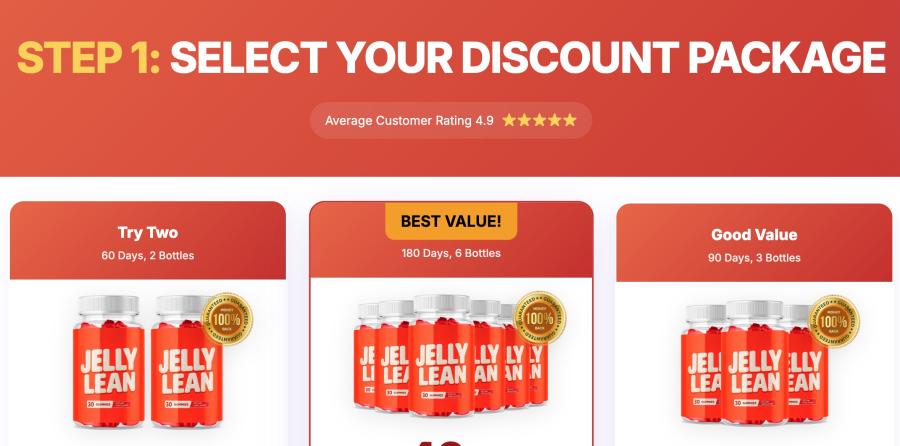
The domain Jellylean.com, the primary site selling these products, shows several red flags:
- Brand New Registration: The site was registered only a few weeks ago, which is unusual for a legitimate brand associated with a high-profile celebrity.
- Hidden Ownership: The domain’s registration is hidden behind privacy protection, meaning there’s no verifiable company contact information.
- Unverified Claims: The site prominently displays FDA and GMP logos, suggesting safety or quality. However, these claims do not prove that the supplement works or that the gelatin trick itself is effective.
These factors make the website highly questionable, and users should proceed with caution.
5. Misleading Video Presentations:
The YouTube reviews also highlighted several suspicious techniques in the promotional videos:
- Fake Progress Bars: Videos often appear long, but the progress bar moves inconsistently, giving viewers the sense they’re near the crucial “secret” portion.
- Emotional Stories: Viewers are shown testimonials and stories of rapid weight loss, creating a sense of urgency and excitement. However, no actual recipe is provided.
- Redirects to Sales Pages: Clicking on video links repeatedly redirects to sales pages, emphasizing product purchase rather than education.
All of these elements indicate that the videos themselves are structured to sell rather than inform.
What’s Actually Real About the Gelatin Trick?
Despite the suspicious marketing, the core concept of the gelatin trick has some legitimacy. The idea is simple ie. consuming protein rich gelatin or collagen before a meal can increase feelings of fullness, which may help reduce overall calorie intake.
How It Works:
- Protein and Volume: Gelatin contains protein and water, which can help increase satiety.
- Timing: The snack is consumed about 15–30 minutes before a meal.
- Simple Homemade Version: Mix unsweetened gelatin or grass-fed collagen with water or juice. Some variations include a small amount of apple cider vinegar.
It is important to note that this approach is not a miracle solution for weight loss. Its effect depends on an individual’s overall diet, lifestyle, and activity level. This information is educational only and is not a recommendation to try any product.
Supplements vs. Homemade Approach:
Products marketed as pre-measured versions of the gelatin trick, like Jelly Lean or Jelly Burn, claim to make it easier to follow the method. However:
- The ingredients and benefits are unverified.
- The marketing suggests unrealistic results beyond what gelatin alone can do.
- FDA and GMP badges may suggest safety, but they do not confirm effectiveness.
The homemade approach is simple, low cost, and educational, but these commercial supplements are not doubt questionable.
The Reality Behind Supplements:
- Offer pre-packaged capsules instead of using natural ingredients.
- Make unverified claims about weight loss and joint health.
- Include marketing gimmicks such as FDA registered facility logos, which do not confirm efficacy.
The core takeaway is that the gelatin trick as a natural appetite curbing strategy is real, but the commercialized products sold online are highly questionable.
Why This Matters:
Understanding the distinction between a legitimate dietary tactic and a suspicious online product is essential:
- Health Risks: Buying unverified supplements carries unknown risks. Ingredients, dosages, and potential side effects may not be properly disclosed.
- Financial Risk: Highly pressured sales tactics encourage bulk purchases of products that may not deliver any results.
- Misinformation: AI-generated ads misusing celebrity images contribute to confusion and distrust in genuinely helpful health advice.
Understanding the difference between legitimate dietary strategies and suspicious marketing is crucial. Consumers should focus on verified, evidence based strategies for weight management, including protein rich snacks, balanced meals, and regular exercise.
Key Takeaways:
- Online promotions for Jillian Michaels’ gelatin trick are highly questionable.
- Misuse of Jillian Michaels’ name and AI-edited videos are strong red flags.
- The actual gelatin trick concept i.e. eating protein rich gelatin before meals is legitimate for appetite management, but it is not a weight loss miracle.
- Homemade gelatin recipes are simple and educational, while branded supplements make unverified claims.
- Always evaluate health claims critically and consult a healthcare professional before trying new dietary methods.
Final Verdict:
The so-called Jillian Michaels Gelatin Trick Recipe for Weight Loss is suspicious and questionable. Ads misusing Jillian Michaels’ image, hidden recipes, unverifiable claims, and pressure sales tactics indicate that the online hype may not be real.
Having said that, the underlying dietary principle ie. using protein rich gelatin before meals to curb appetite is a legitimate, simple, and cost effective approach to support weight management but it should be used as part of a balanced diet and active lifestyle, not as a standalone miracle solution.
Always consult a healthcare professional or nutritionist before introducing new dietary supplements or making significant changes to your diet. And remember Jillian Michaels’ warning i.e. any product claiming her endorsement other than of @alaya.naturals should be treated as highly suspicious.
Disclaimer: This article has been written by a Scam Fighter Contributor. If you believe the article above contains inaccuracies or needs to include relevant information, please contact ScamAdviser.com using this form.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if