Gift Card Scams
Author: Nichlaus O.
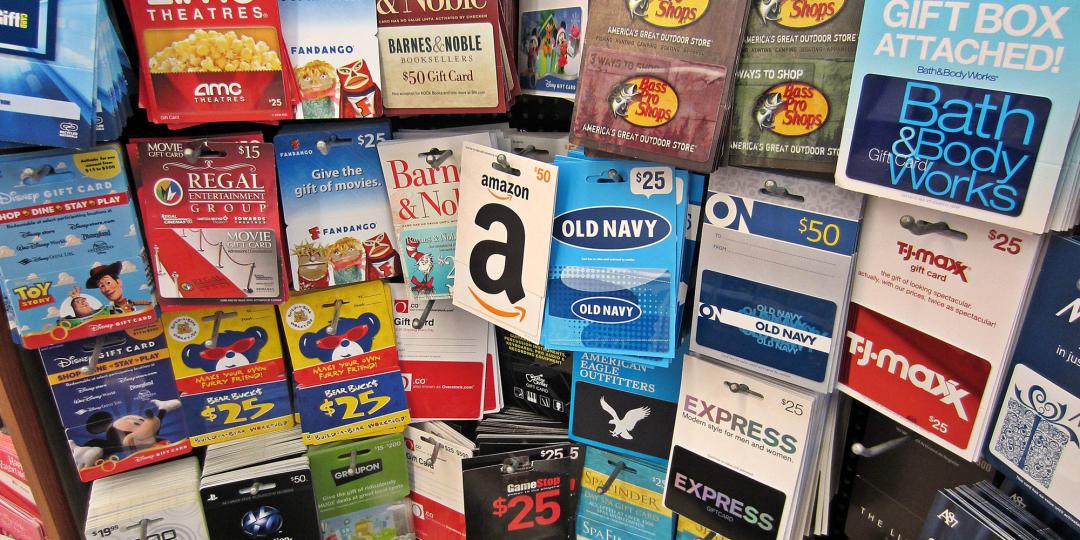
A gift card is intended to be used in exchange for goods or services offered by the issuer. You shouldn't take it as a normal form of payment. Any seller who insists on a gift card payment is most likely a scammer.
Scammers love gift cards because they are NOT traceable. That should give you a hint of why scammers invest time and energy to these scams here.
Gift Card Payments over Cash
Have you ever been asked to pay for any good or service by a legitimate business? Paying for things through gift cards thrives in online platforms where sellers are individuals you can't meet.
Walmart, iTunes, eBay, and Google have several retailers that sell their gift cards.
Scammers will contact you claiming to be tech support, IRS agents, lottery official, or any other recognized official. They claim you owe a debt that should pay for in gift cards. Then ask that you send the code at the back of the card.
Some will call and claim that you have already used a service. And you should pay through gift cards. Hang up and ignore such calls in the future.
Other online shopping scammers offer goods online at great bargain prices and insist that you pay through gift cards. Once you give them the gift card code they go silent on you and the money in the card vanishes!
There have also been charity scams connected to gift cards. Scammers posing as clergymen raising money for a worthy cause or a congregant in need. They call, text, or email the worshippers and ask them to buy gift cards then share their numbers.
The government and companies worth their salt do not ask for payment through gift cards. They ask for payment in real money.
Clever Gift Card PIN Theft
Some fraudsters are so bold as to visit stores that sell gift cards and instead of buying, they scratch to reveal the PIN, take a photo and put a sicker back on. Such a card will not appear damaged to your undiscerning eye. You will only realize that it's bogus after buying and trying to use it!
The scammer stole the PIN code but left the card. Only the PIN is necessary for exchanges.
Pay for Gift Card Shipping
It is common for scammers to pose as genuine company representatives. A Walmart gift card scam showed buyers being baited through an email. "Take part in a survey and you could win a $500 gift card", the email said.
Here's the catch: send $1 for shipping. Please don't. It's a scam.
If you have won a gift card worth $500 why should there be a cost for sending it to you? There shouldn't be. But this was an Advance Fee scam all along. Don't fall for it.
Phishing eGift Card Email
If you get an email that you've won an electronic gift card, please do not click on the link given to claim it! Such emails will lead you to lose your personal information without knowing. The link given to "claim" your gift card will lead to 2 things:
- A site where you need to input your personal information, OR,
- A prompt to download and install software.
None of these are options you should take when online. Avoid them, they are most likely scam in the making.
Warning Signs of a Gift Card Scam
- Tampered gift card packaging.
- The insistence by a seller to pay through a particular retailer's gift card.
- Some more scam signs.
If You Fall Victim to a Gift Card Scam
- Report to the Federal Trade Commission (FTC)
- Report the scam details to the gift card issuer
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if