Survey Suggests China Not Just Biggest Manufacturer but Biggest Seller of Fakes Too

ScamAdviser.com surveyed 1,494 consumers from across the world asking them why they buy fakes and how they could be kept from buying counterfeit.
While all income groups, educational categories, age levels and continents are represented, it is interesting to note that mostly men (67%) participated. This trend is identical to the previous year's survey, where 65% of the participants were men, suggesting that men may be buying more counterfeit than generally thought.
Fake goods are estimated to exceed $500 billion annually
According to OECD, 3.3% of world trade is now the trade in fake goods. Footwear made up almost a quarter of seized goods around the world, making it the most popular product copied by counterfeiters. But also apparel & accessories, leather goods, perfumes, electronic devices and watches.
69% say they are good at identifying fakes
Most consumers (69%) consider themselves capable of identifying counterfeits. This is especially the case for Clothing, Accessories and Consumer Electronics. Only 10% admit they are unable to identify fakes. 45% of consumers doubt their ability to recognize fake Medicines and Toys while 23% say they have trouble with all categories.
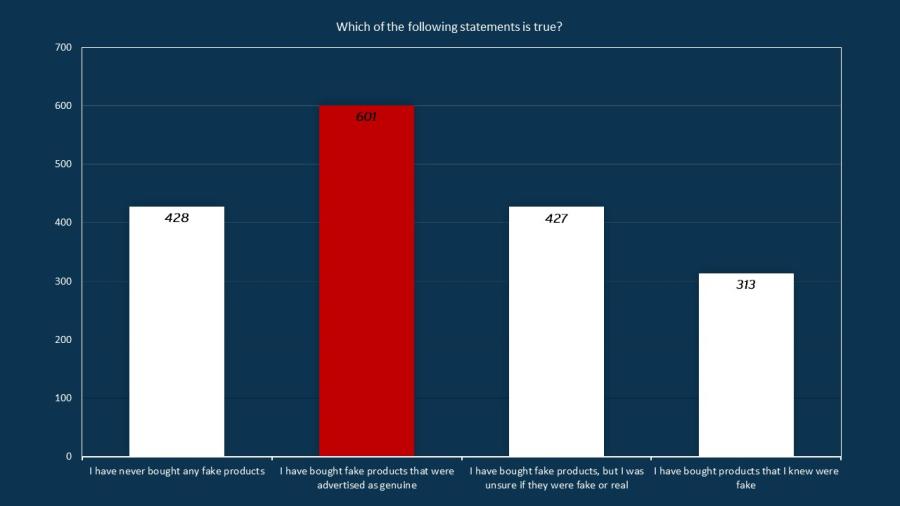
92% of all consumers have bought counterfeits
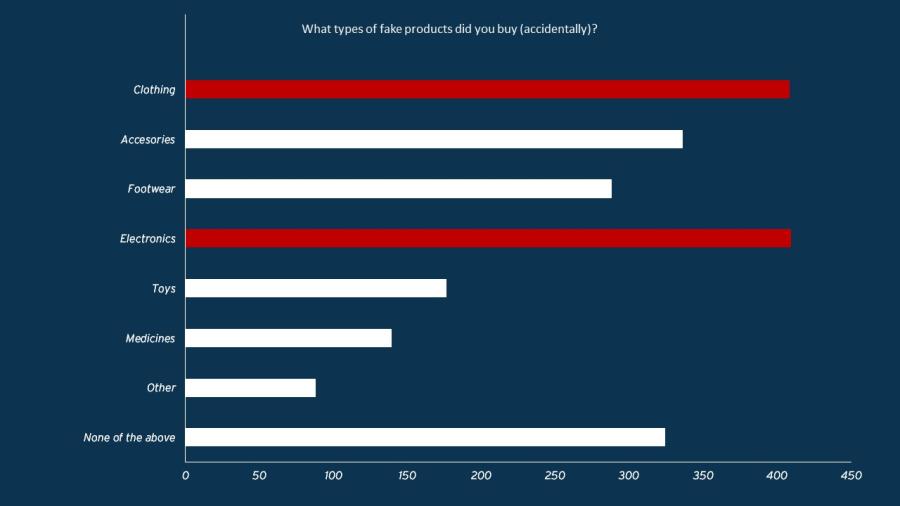
Still, 70% of the consumers have bought a fake product in the past unknowingly or doubting the originality of the product. 21% admit to knowingly having bought fakes. Clothing, electronics and accessories are the most commonly purchased fake products.
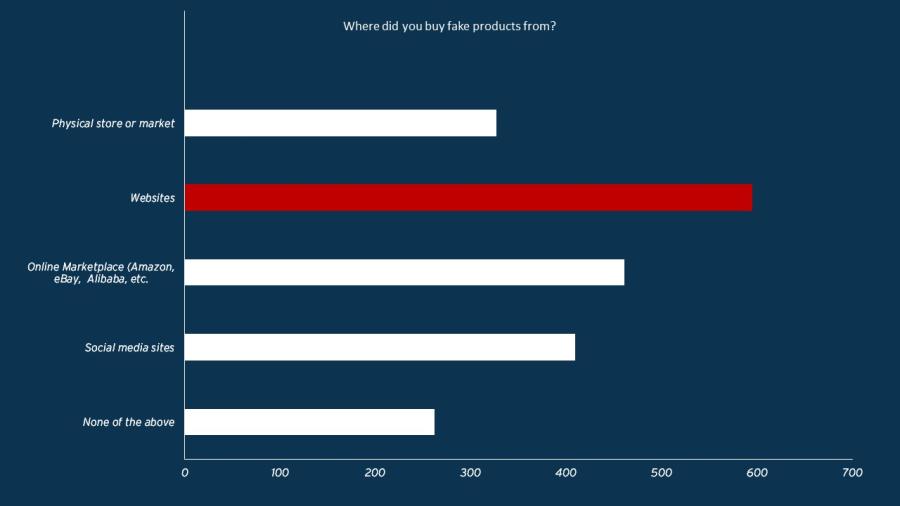
Websites, not marketplaces, are the main purchase channel
The focus of brand protection agencies has shifted to online marketplaces in recent years. However, remarkably, websites (41%) are by far the most popular channel to buy counterfeits. This channel is followed by online marketplaces like Amazon, eBay and Alibaba (32%).
Social media sites are named by 28% of consumers and 22% bought fakes from physical stores. Physical markets and stores are slowly losing popularity while buying directly via Social Media is on the rise (but not yet as big as websites).
39% think that the fakes are sold directly from China
When asked to name the originating selling country of their fake goods, 39% of consumers named China. This was followed by, surprisingly, the United States (9%) and India (6%).
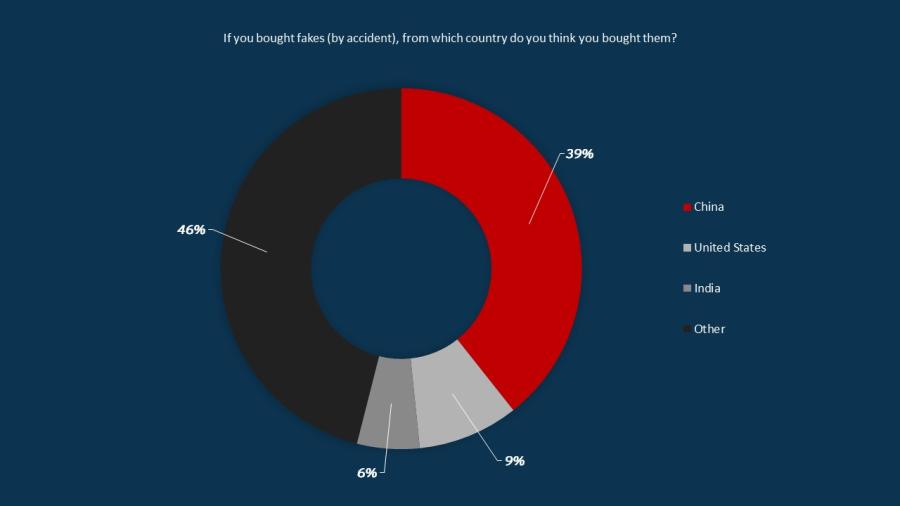
According to an OECD report, the majority of fake goods picked up in customs checks originate in mainland China and Hong Kong. Other major points of origin include the United Arab Emirates, Turkey, Singapore, Thailand and India. However, a large number of consumers have named their own countries, indicating that they are being misled into believing that the fake goods they buy are originating in their own countries.
Consumers are dissuaded by fears, not ethics
Consumers buy fakes primarily as they believe that there will be no significant difference in quality (16%). Affordability (16%) is an equally big motivator for buying fakes and the feeling that the real brand is overpriced (12%) is also named.
Consumers are aware that counterfeits support crime and human exploitation. What however would keep consumers the most from buying counterfeit is the concern about the quality of the product (42%) and the belief that buying fakes online is not safe as their (financial) data may be misused (38%) and the product not being delivered (32%).
Regarding the fight against counterfeits, consumers think the lead should be taken by consumer protection agencies (49%) and not by international authorities such as Europol/Interpol (25%) and the EU/UN (24%).
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if