Recovery Scam: Fraud After the First Scam
Author: De-Reviews.com Team
A recovery scam is one of the most dangerous types of fraud targeting people who have already been scammed. These scammers approach victims claiming they can help recover lost money, but in reality, they are the same fraudsters or a new group preying on vulnerable individuals. The goal is to steal even more money from victims who are already emotionally and financially affected by their first loss.
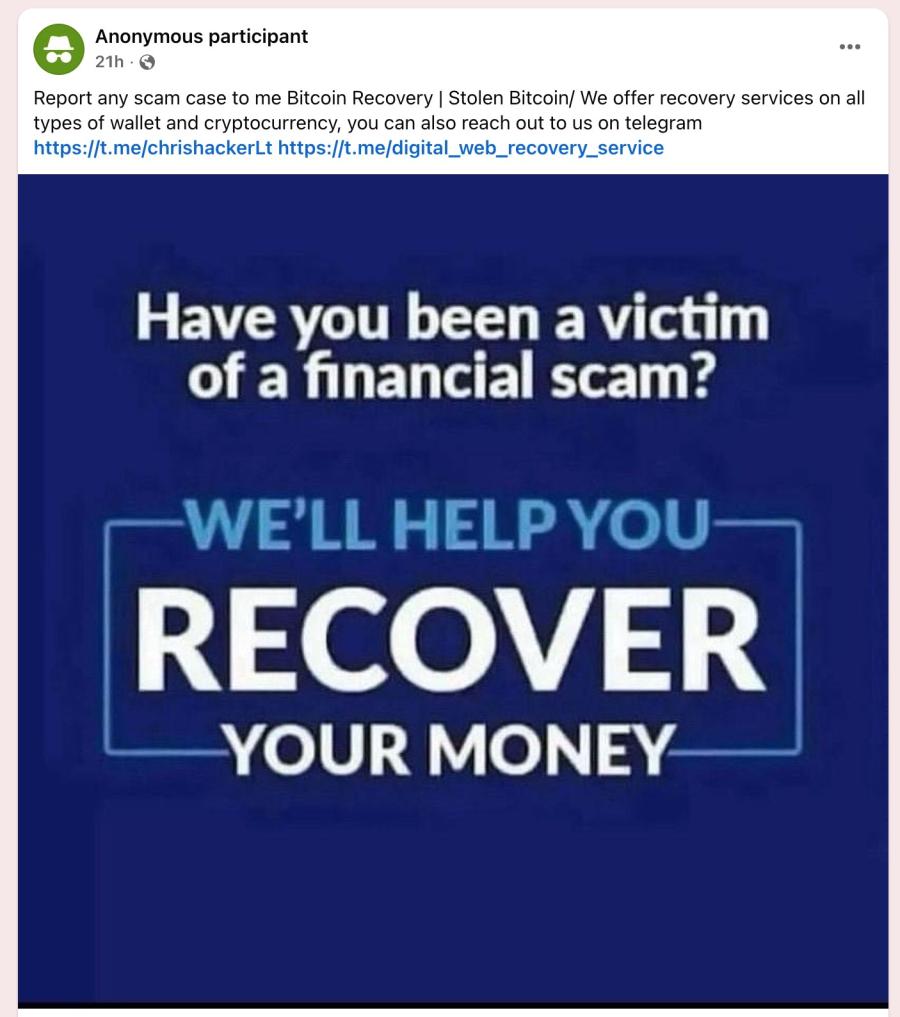
Recovery scams can appear in many online places, including social media posts, comment sections of scam-related articles, private messages, emails, or even chat apps like WhatsApp and Telegram. Scammers often craft messages that look like genuine experiences of past victims, making their claims seem credible. They may even provide an email address or phone number for the supposed “recovery expert”, encouraging victims to reach out.
Unfortunately, these scammers never recover the money. Instead, they exploit victims by requesting upfront payments, personal information, or even remote access to devices. Once the victim complies, the scammers vanish, leaving the victim worse off than before.
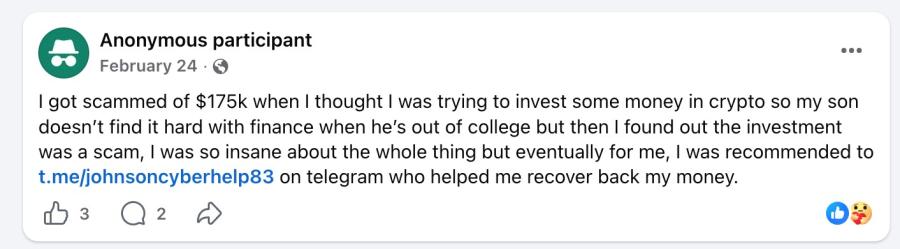
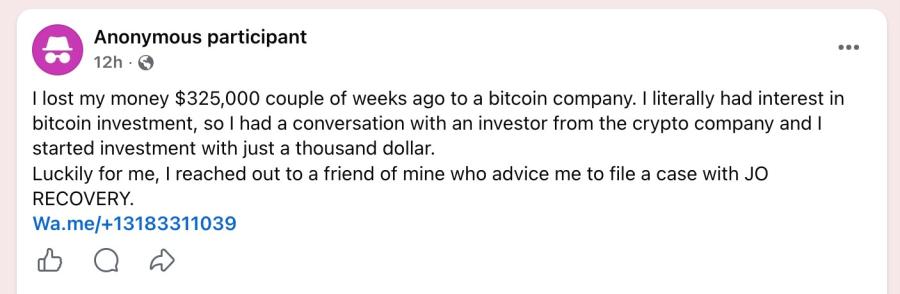
Examples of Recovery Scam Messages:
Below are examples of the kind of messages used to lure victims:
"Everyone should be careful, it was actually painful when I dicovered i was scammed by PRIMECFDs and Carlosfxtrade with over $125,000 but Mr Alfred Bernard helped me to recover my invested capital with my profit. Feel free to contact him on his private email address: alfredbernard 799 @ gmail . com for assistance."
"I’m posting this review to warn others about cryptO investment scams that are becoming more common online. Scammers often create professional-looking websites and pretend to be financial experts to gain your trust.They will show you fake profits to encourage you to invest more m0ney, but when you try to withdraw your funds they demand additional payments such as taxes, verification fees, or withdrawal charges. If you encounter something like this, stop immediately and do not send more money. Always verify the legitimacy of any investment platform and report suspicious activities to the proper authorities. Good to see a review about this great Hacker Brunoe Quick Hack, If you have been scammed by crypt0 investment, Don’t panic—you’re not alone. Brunoe Quick Hack Thanks to their skills and persistence, I finally recovered my stolen Crypt0 Contact: BrunoeQuickHack (@) GMAIL.COM
WhatsApp +1705-(7842-635)
Stay safe and always do your research before investing online."NOTE: The information provided in the above examples may be impersonated.
How Recovery Scams Work?
Scammers often use sucker lists, which contain details of people who have already lost money to previous scams. They target these individuals with personalized messages, making the victim feel understood and hopeful. Common tactics include:
- Claiming they can recover the money lost in a previous scam.
- Pretending to be lawyers, government officials, law enforcement, or cybersecurity experts.
- Requesting upfront payments, including processing fees, taxes, or retainer fees.
- Using fake testimonials or stories that show successful recoveries.
- Asking victims to pay using cryptocurrency, gift cards, or wire transfers.
- Pressuring victims to keep the recovery process confidential.
In some cases, scammers target cryptocurrency victims with fake wallet addresses or recovery tools, claiming that funds are stuck and require a fee to release. This method ensures that victims never get their money back.
Platforms Where Recovery Scams Appear:
Recovery scams are increasingly common in online spaces where victims of prior scams discuss their experiences. Some of the most common places include:
- Comment sections of websites reporting on scams.
- Social media posts warning about scams or sharing scam experiences.
- Email messages and direct messages claiming to be from recovery companies.
- Messaging apps such as WhatsApp, Telegram, or SMS.
Scammers strategically position themselves in these spaces to appear trustworthy, often using personal details from victims’ public posts to gain credibility.
Key Warning Signs of Recovery Scams:
Victims should watch out for the following red flags:
- Unsolicited contact from someone claiming to help recover previously lost funds.
- Requests for upfront fees before any recovery work begins.
- Guaranteed results, promising that the money will be recovered without fail.
- Unusual payment methods, such as cryptocurrency, gift cards, or wire transfers.
- Pressure for secrecy, asking the victim not to tell anyone about the process.
Being able to recognize these warning signs is critical to avoid falling victim to a recovery scam.
How to Protect Yourself?
Preventing recovery scams requires vigilance and careful action. Key steps include:
- Never pay for recovery services. Legitimate authorities and law enforcement agencies do not charge victims upfront to investigate or recover lost funds.
- Do not provide personal information such as bank account numbers, Social Security numbers, or login credentials to anyone claiming to help.
- Verify identities independently. If someone claims to be a government agent, lawyer, or recovery expert, find official contact information and confirm their legitimacy.
- Report suspicious activity to local law enforcement or consumer protection authorities.
- Contact your financial institution immediately if you have already sent money to a suspected recovery scammer.
- Organizations specializing in fraud awareness and prevention can also provide guidance and support to victims.
Final Thoughts:
Recovery scams are especially harmful because they target people who are already vulnerable after being scammed once. These scams rely on hope and trust to extract even more money and personal information. Victims must remain vigilant, question any unsolicited recovery offers, and always verify before taking action.
Remember, if someone promises to recover your lost funds for a fee or asks you to pay before any work is done, it is almost certainly a scam. Awareness, careful verification, and prompt reporting are the most effective defenses against these fraudulent schemes. Protect yourself, stay informed, and do not let scammers take advantage of your previous losses.
Image Source: Pixabay
Disclaimer: This article has been written by a Scam Fighter Contributor. If you believe the article above contains inaccuracies or needs to include relevant information, please contact ScamAdviser.com using this form.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if