TarGifted.com Investigative Review: The $700 Gift Card Trap
Author: Adam Collins
In a Nutshell
- Newly registered site with no proven reputation
- Requires paid “tasks” to unlock rewards
- Collects sensitive personal data early in the process
- No real connection to Target or official promotions
A $700 gift card for completing a few simple tasks sounds like easy money. That’s exactly what TarGifted.com promises—and why it’s spreading quickly across platforms like TikTok and Instagram. But once you look closer, the offer starts to unravel.
The domain TarGifted.com was registered on January 8, 2026. Despite this recent launch, the site presents itself as part of a large promotional ecosystem tied to a major retailer. In reality, there is no verified connection to Target Corporation. That disconnect is where the risk begins.
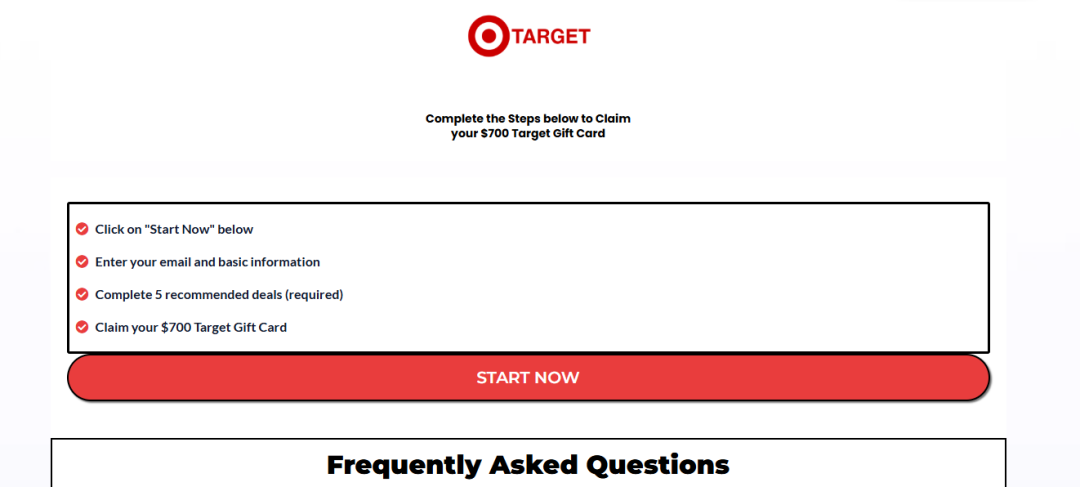
How Does the “$700 Gift Card” Offer Work?
At first, the process looks simple. You enter your details, complete a short survey, and expect to claim your reward. But instead of a quick payout, you’re pushed into a system of “Deals” or tasks.
These tasks often include signing up for subscriptions, downloading apps, or making small payments. To qualify for the reward, you’re required to complete multiple offers—sometimes 15 or more. By the time you reach the final stages, you’ve likely spent both time and money chasing something that was supposed to be free.
This setup is designed to keep you engaged. The more you complete, the harder it becomes to walk away, even when things start to feel off.
What is the “Task Trap”?
This model is often referred to as a task-based or reward funnel system. It relies heavily on psychological pressure.
As you progress, you may feel compelled to keep going because you’ve already invested effort or money. This is known as the “sunk cost” effect. Instead of cutting losses, users continue completing tasks in the hope that the reward is just one step away.
In reality, many users never reach a successful payout.
What Happens to Your Personal Data?
One of the biggest concerns isn’t just the money—it’s your data.
TarGifted.com requests personal details such as your name, phone number, and address early in the process. Without a transparent company behind the site, there’s no clear accountability for how this information is stored or shared.
Providing your phone number may also expose you to ongoing spam calls or messages. Some users unknowingly consent to marketing terms that allow third parties to contact them repeatedly.
Is TarGifted.com Really Linked to Target?
No—and this is a critical point.
Legitimate promotions from Target Corporation are hosted on official channels or verified partners. They don’t rely on newly created third-party websites with unclear ownership.
Using a well-known brand name is a common tactic to build instant trust. It lowers your guard and makes the offer feel more legitimate than it actually is.
If a company were genuinely giving away $700 gift cards at scale, it wouldn’t be limited to a single unfamiliar website. We have seen similar thing with $100 McDonald’s Gift Card scam.
Do Users Actually Get Paid?
This is where many reports raise concerns.
Even after completing numerous tasks, users often face issues during the final stages. Accounts may be flagged, progress reset, or verification steps may fail without clear explanation.
Some sites also use fake activity indicators—like “recent winners” or countdown timers—to create urgency and social proof. These elements are often pre-programmed and not based on real user activity.
What Should You Do If You Already Signed Up?
If you’ve interacted with the site, it’s important to act quickly. Monitor your bank statements for unexpected charges, especially if you signed up for any “trial” offers.
You should also keep an eye on your phone and email for increased spam activity. If anything suspicious appears, consider blocking numbers or reporting them.
If you shared financial details, contacting your bank to secure your account is a smart move.
Bottom Line: Is TarGifted.com Legit?
Overall, we have doubts about TarGifted.com.
- TarGifted.com is not affiliated with Target
- Requires completing paid tasks with no guaranteed reward
- Designed to collect personal data and generate revenue
- Users often report not receiving promised payouts
- High risk with little to no transparency
TarGifted.com follows a familiar pattern: a high-value reward, a simple entry point, and a long chain of requirements that rarely lead to a real payout. What looks like an easy win is often just a system designed to profit from your time, data, and small payments along the way. Read more on gift card scams.
This article has been written by a scam fighter volunteer. If you believe the article above contains inaccuracies or needs to include relevant information, please contact ScamAdviser.com using this form.
Adam Collins is a cybersecurity researcher at ScamAdviser who operates under a pseudonym for privacy and security. With over four years on the digital frontlines and 1,500+ days spent deconstructing thousands of fraud schemes, he specialises in translating complex threats into actionable advice. His mission: exposing red flags so you can navigate the web with confidence.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
In a nutshell: A good VPN protects your privacy with strong encryption, a strict no-logs policy, and fast protocols like WireGuard. The best VPNs also offer wide server coverage, leak protection, and easy-to-use apps for all devices. For 2025, the top providers are NordVPN, ExpressVPN, Surfshark, Proton VPN, Private Internet Access, CyberGhost, and Mullvad—each excelling in speed, security, or value. In an age where every click is tracked, a Virtual Private Network (VPN) is no longer just a luxury—it's an essential tool for digital privacy and security. A VPN works by creating a secure, encrypted tunnel between your device and the internet, masking your real IP address and protecting your sensitive data from prying eyes. But with hundreds of providers out there, how do you sort the secure from the suspect? This guide breaks down the non-negotiable features of a quality VPN and highlights the 7 top-rated services for 2025. What to Look for in a Good VPN: The 4 Non-Negotiable Pillars 1. Ironclad Security Features Strong Encryption: AES-256, the gold standard. Secure Protocols: OpenVPN, WireGuard, NordLynx, Lightway. Avoid PPTP. Kill Switch: Ensures no accidental IP leaks. Leak Protection: Covers DNS, IPv6, and WebRTC. 2. Verified Privacy Practices No-Logs Policy: No activity or metadata tracking. Independent Audits: Verification by third parties. Safe Jurisdiction: Prefer countries outside the 5/9/14 Eyes alliances. 3. High-Speed Performance Fast Protocols: WireGuard and equivalents. Large Server Network: Less crowding, more reliable speeds. 4. Essential Usability Features Multi-Device Apps: Windows, Mac, iOS, Android, routers. Simultaneous Connections: One account, many devices. Unblocking Power: Netflix, Hulu, BBC
How to Protect Yourself and Your Family After a Data Breach When Your Data Falls Into the Wrong Hands Just received that terrifying notification? Or perhaps you've noticed suspicious activity in your accounts? Take a deep breath. A data breach, the unauthorized access or exposure of sensitive, protected, or confidential data, is a deeply unsettling event. It can plunge you into a world of worry, bringing risks from financial losses and identity theft to significant emotional distress and reputational damage. The numbers don't lie: according to a 2024 report, the number of data breach victim notices has grown by a staggering 211% year-over-year. This isn't just a distant threat; it's a stark reality many individuals face. This year alone, we've seen major organizations like Adidas and Qantas grapple with high-profile data breaches, affecting countless customers. This underscores a critical truth: nobody is untouchable. Subsequently, strategic action is the only way to minimize the risk and protect your future. This guide is your emergency action plan, designed to walk you through every crucial step—from confirming the breach to fortifying your digital life for the long term. Part 1: Confirming the Breach and Understanding the Damage The very first step is to answer the question definitively: Was my data compromised, and if so, how badly? Start with the basics: Check Official NotificationsReputable companies are legally obligated to inform you if your data was part of a breach. Look for official emails, letters, or public announcements. Check Verified Breach DatabasesPlatforms like HaveIBeenPwned help you see if